3. Secure Boot
3.1. Security features
DA1459x SoC devices support a number of security features that can be configured. This is done using the configuration script to program a number of special bits in the SECURE_BOOT_REG (0x500000CC).
Note
Since the DA1459x SoCs have no OTP, these special security bits in the SECURE_BOOT_REG are so called set-once (sticky) bits, which means that once they are set, they can only be reset by a hardware- or POReset.
Bit Field |
Description |
|---|---|
FORCE_M33_DEBUGGER_OFF |
This bit permanently disables the M33 debugger |
FORCE_CMAC_DEBUGGER_OFF |
This bit permanently disables the CMAC debugger |
PROT_USER_APP_CODE |
This bit permanently disables write/erase operations on sector 5-12 (Customer Application Area) in the embedded Flash. |
PROT_APP_KEY |
This bit permanently disables read/erase operations on sector 2, address range 0x00000800-0x00000BFF (User Application Expanded Encryption Keys) in the embedded Flash. |
PROT_VALID_KEY |
This bit permanently disables write/erase operations on sector 2, address range 0x00000C00-0x00000FFF (Signature Keys) in the embedded Flash. |
PROT_CONFIG_SCRIPT |
This bit permanently disables write/erase operations on sector 1 (User Configuration Script and security keys pointers) in the embedded Flash. |
SECURE_BOOT |
This bit enables authentication of the image in the embedded Flash while the system is booting. |
3.2. Secure Booting
Secure boot is enabled by programming the SECURE_BOOT_REG[SECURE_BOOT] bit in the User Configuration Script and security keys pointers sector. This forces authentication of the eFlash image before booting is finished. The booter code starts the Doubler, switches the system clock to 64 MHz, and then executes the Ed25519 verification algorithm. If the generated signature and the signature stored in the eFlash match, authentication is successful and booting is continued. If not, a hardware reset is issued.
Note
The secure boot feature is not supported when booting from QSPI Flash is selected.
Besides setting the security bit in the SECURE_BOOT_REG also the signature key(s) and index table(S) need to be programmed.
3.3. Secure Keys Mechanism
This feature allows for programming up to eight different 256-bit symmetric keys for the user application cases and up to eight different 256-bit ECC keys for the authentication of the embedded Flash image.
A revocation mechanism is supported through the ROMbooter, allowing for changing the current key of any of the two operations while the product is in the field.
For each product key there is a product key index, 4-bytes each, that designates the validity of that specific secure key. By default, the value of all key indexes is 0xFFFFFFFF. In fact, this is the value of an unwritten eFlash memory cell. A key index value set to 0xFFFFFFFF designates a valid product key whereas, a key index value set to 0x00000000 designates a revoked and hence an invalid product key.
Attention
To increase security even further, it is possible to create one symmetric key specific to each device and store it (in OTP slot 8) in the User Data Encryption Key Area. This key can be used to encrypt and decrypt local stored application data and (locally stored) bonding data.
3.4. Secure access
To make the devices even more secure it is advised to permanently disable the SWI (JTAG) interface to prevent unwanted access to the DA14592 CPUs. This is done by programming the SECURE_BOOT_REG[FORCE_M33_DEBUGGER_OFF] and SECURE_BOOT_REG[FORCE_CMAC_DEBUGGER_OFF] in the configuration script. This disconnects the SWI signals from the respective CPU’s SWI controller. Except for the sticky bit, the debugger has its own enable bit, namely, SYS_CTRL_REG[DEBUGGER_ENABLE] which is by default disabled. This bit is enabled during booting at the “Retrieve Application Code” phase.
If nothing is programmed in the configuration script, JTAG is enabled a few microseconds after POWERUP. If the sticky bit is programmed, JTAG is permanently disabled.
3.5. Key protection
The application- and validation keys can also be protected by programming the SECURE_BOOT_REG[PROT_APP_KEY] and/or SECURE_BOOT_REG[PROT_VALID_KEY] respectively.
3.6. eFlash secure area
The first 2 sectors (2 x 2kB) of the eFlash are used to store the User Configuration Script and the keys:
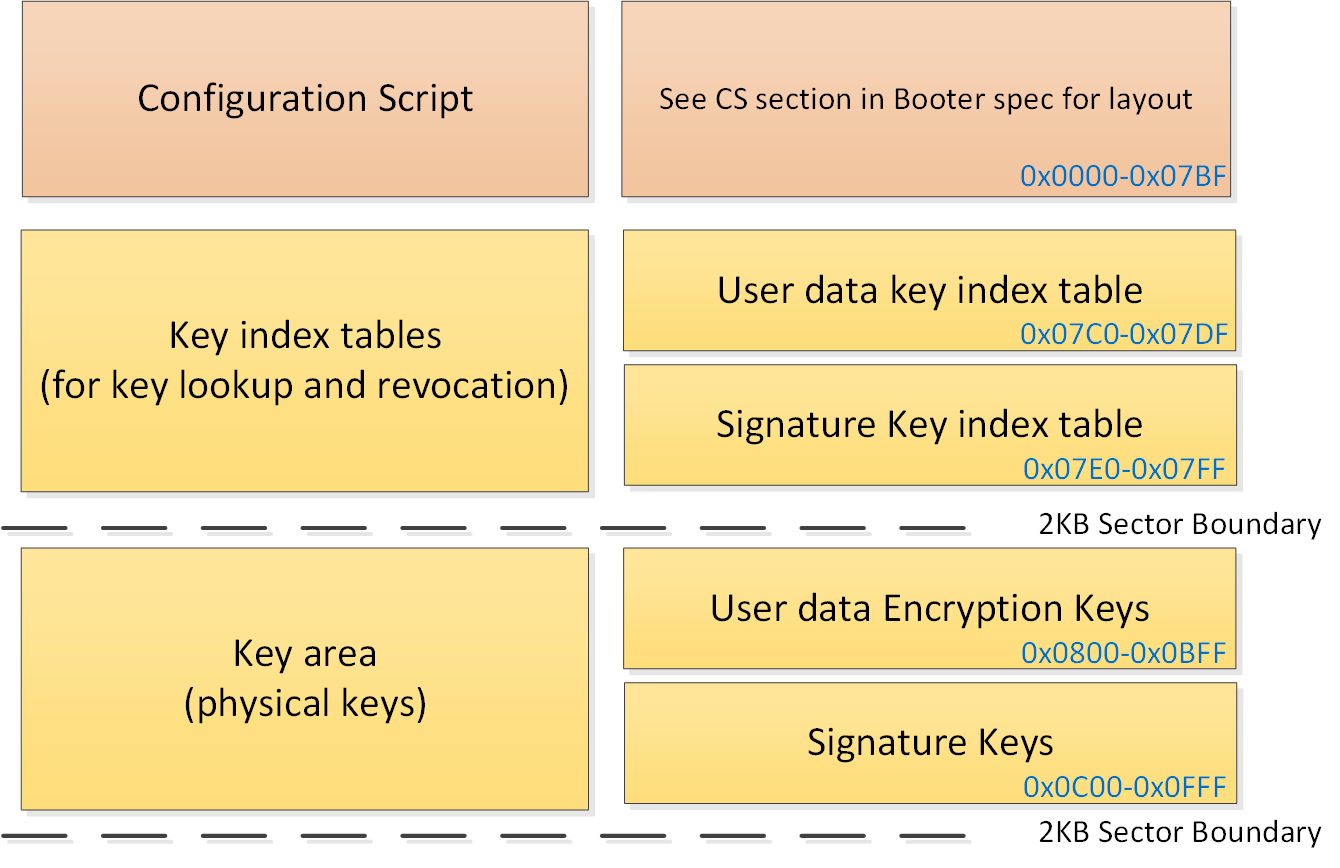
Figure 1 Configuration Script / Key Area