1. Introduction
1.1. Before we start
This tutorial will give a basic understanding of Bluetooth Low Energy (BLE) security. We will see how two devices can exchange information between them so that they can set up an encrypted link, what are the encryption schemes that are part of the BLE specification, and how we can utilize the full potential of Renesas SDK6 for secure data transfers.
Before beginning with this tutorial you should download the latest SDK under SDK . Additionally, a DA14531 Pro Development kit or DA14535 Pro Development kit is required for running the example in this tutorial.
1.2. Some basics of cryptography
Protection of private information is important for every wireless low energy device, from fitness bands to payment systems. In today’s world, technology can help us improve our everyday lives substantially, but at the same time we have to be very cautious about the risks to which it may expose us. Producers of consumer electronics should prioritize on the security features of their devices and implement robust security mechanisms and best practices. Privacy considerations are also of major importance, as the use of personal devices could expose users to the risk of being tracked and consequently leak information on their personal preferences.
1.2.1. Symmetric and private-key cryptography
The purpose of cryptography is to enable the transmission of private information over a communication link that is not secure. That means that there could be a third-party who inspects the medium and we want to make sure that only a trusted end will be able to read the original message. For this purpose we have to transform our sensitive piece of information, which we’ll call the plaintext, into an unreadable string of characters, called the ciphertext.
In general, there are two cryptography schemes, symmetric-key cryptography and public-key cryptography. In the first case, when two people want to exchange private information, they must first agree on a common secret key which they will both use to encrypt and decrypt their data. In public-key cryptography (also called asymmetric cryptography) each party generates its own pair of a public key and a private key. Both parties exchange their public keys and keep their private keys secret. The most notable key exchange scheme is called the Diffie–Hellman key exchange. When each party receives the public key of the other end, it mixes it with their own private key and that results in a shared secret key. This shared secret key can then be used to encrypt a private message as in the case of public-key cryptography.
Elliptic Curve Diffie–Hellman (ECDH)
The Bluetooth Specification 4.2 introduced the LE Secure Connections pairing which uses the Elliptic Curve Diffie–Hellman(ECDH) key exchange. Elliptic Curve Cryptography is regarded as a very secure cryptography scheme in terms of its computational complexity and intractability, while being very well-suited for constrained devices with low processing power and memory size.
1.2.2. Security attacks
To be better protected of potential security attacks, we must first understand which are the methods that a malicious party could use to compromise our privacy or the integrity of the messages.
Passive attacks: In this type , Alice and Bob want to communicate privately, but the channel by which they are communicating is eavesdropped by Eve. Since Eve could been eavesdropping on the message exchange from the start, the key and message exchange process shouldn’t expose any information from which Eve could derive the keys, or she could be able to decrypt the messages and produce the plaintext.

Figure 1 Passive eavesdropping
Active attacks: In this scenario, Alice and Bob think that they are talking with each other directly, but in fact Eve is acting as the middle-man and she may relay the messages or alter them in order to trick them into revealing information that could expose the link keys. This type of attack is called a man-in-the-middle (MITM) attack.
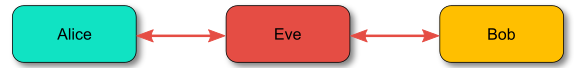
Figure 2 Man-in-the-middle attack
Since a lot of electronic equipment is designed to be carried by the user, tracking a device could pose the risk of tracking the person that owns it. The location of an individual constitutes private personal information and it could imply a lot on their personal preferences. In this tutorial, we will take an in-depth look on the provisions of the Bluetooth specification that limit a malicious party’s attempts on hacking a device and how we can enable them using Renesas’s SDK6.
Transmission medium
The transmission medium also plays an important role of the security of the overall communication system. Wireless transmissions are very prone to attacks, as the attacker could be anywhere in the transmission range, which could be over 100 meters, based on the specification used.